In a surprise raid on Thursday, October 30, 2025, Russian law enforcement detained three individuals suspected of creating and selling the malicious Meduza Stealer. The arrests took place in Moscow and the surrounding area, following an investigation from the Investigative Department of the Ministry of Internal Affairs of Russia, as confirmed by Irina Volk, spokesperson for Russia’s Interior Ministry.
Meduza Stealer’s Profile and Pricing
The suspects, described as ‘young IT specialists,’ allegedly ran Meduza as a profitable Malware-as-a-Service (MaaS) operation since mid-2023. This notorious C++-based program quickly became a powerful information stealer, capable of gathering sensitive data, including:
- Login Credentials: Passwords and session tokens from over 100 browsers and 27 password managers.
- Cryptocurrency: Data from over 100 wallets, including browser-based extensions.
- Messaging/Gaming: Information stolen from Telegram IM and Steam clients.
The malware was actively sold on underground forums and Telegram channels. Subscription pricing for the latest version, Meduza 2.2, was set at $199 per month, with a lifetime membership costing $1,199. It was also highly sophisticated, using the ChaCha20 algorithm for payload encryption and anti-VM features to bypass security analysis.
Investigation Details- The Critical Error
The investigation’s key turning point was the group’s alleged decision to breach a Russian government organisation in the Astrakhan region earlier this year and steal classified data. This attack was perhaps a fatal error because Meduza Stealer was specifically designed with a geo-filter to avoid targets in Russia, Kazakhstan, and Belarus, a critical operational security (OpSec) rule among local cybercriminals to maintain an implicit shield from authorities.
The Dramatic Crackdown
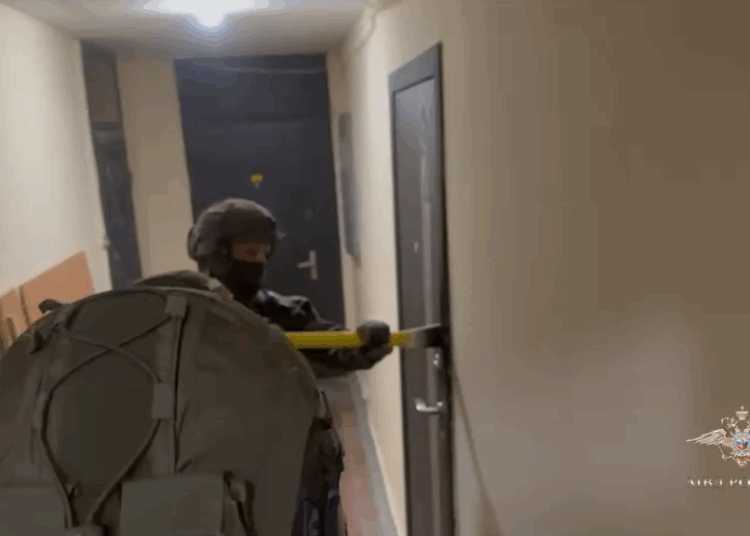
Police seized computer equipment, phones, and bank cards during the raids. The Video footage of the operation, conducted with the support of Rosgvardia forces, shows officers storming multiple apartments, and one suspect is filmed wearing ‘Hello Kitty’ pajama pants
“Three defendants have chosen various preventive measures. All accomplices and episodes of illegal activity are established,” said Volk.
Investigators also discovered the group had developed a second, unidentified piece of malware designed to disable security defences and build botnets. If convicted on all charges, the three young specialists face a potential prison sentence of up to five years.
This arrest signals a clear and consequential change in Moscow’s stance. According to a recent report from Recorded Future’s Insikt Group, Russia’s strategy toward the local hacking scene is moving from passive tolerance to active management.
These arrests validate the finding that Russia is using selective arrests and public crackdowns to assert state authority and target domestic hackers who become too visible or politically inconvenient.