The recent revelations by Le Monde, involving members of the security teams of several heads of state, highlight a crucial issue in mobile security: how an apparently harmless app like Strava can turn its users’ privacy into an exploitable vulnerability, threatening not only their safety but also that of those around them.
The Stravaleaks case demonstrates how the use of the Strava app enabled journalists to predict the future movements and meeting locations of political figures such as Presidents Emmanuel Macron, Joe Biden, and Vladimir Putin.
This investigation shows that an app does not need to be designed with malicious intent to pose a security risk, and that cybersecurity awareness has its limits.
Recreational Apps: A Major Threat in a Professional Context
Strava, the popular fitness-tracking app, is not malicious. However, its model is based on collecting and sharing location data, allowing users to track their routes and interact with others. In an anonymous context, this usually has minimal consequences. But when this data is identifiable, it reveals near real-time movements, routines, strategies… When such information is linked to high-ranking government officials, political figures, or other leaders or public personalities, it exposes them to the risk of espionage, cyber and physical attacks.
Raising Awareness Among Mobile Users Is Not Enough to Ensure Security
Despite awareness and training efforts, the understanding of risks related to mobile use remains insufficient, even in the most exposed environments. While heads of state and senior officials are often surrounded by sophisticated security teams, the use of certain personal tools, such as health or fitness-tracking apps, is still not perceived as a potential security threat. No sector is immune, as mobile devices are still often mistakenly seen as inherently secure by their users.
Mobile Devices Require Dedicated Security to Control Data Disclosure
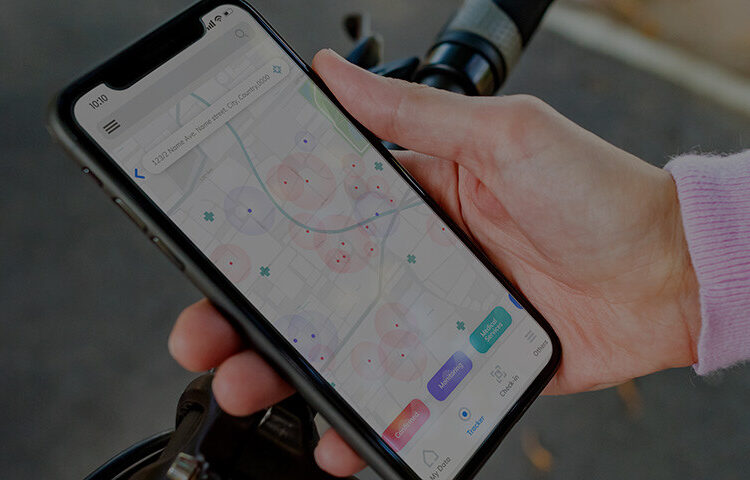
The Stravaleaks case raises a crucial question: how do we protect mobile user data, especially when it is highly sensitive in a given context? The solution to this problem lies in three key capabilities: identifying potential data access, contextualizing it, and blocking it if it poses a threat.
At Pradeo, we understand that each user and usage context is unique. Pradeo’s mobile fleet protection solution offers contextual mobile security, adapting to the realities of users and the confidentiality requirements of all sectors. Thanks to behavioral analysis technologies, our solution identifies security events occurring on mobile devices, including those triggered by applications. It then cross-references them with the security requirements of each user organization. By ensuring continuous and autonomous protection of mobile devices, our solution enables organizations to maintain control over their data, even when recreational apps are used in a professional context.
This recent news is just the latest example of a mobile security breach stemming from an otherwise harmless app. It underscores the urgent need to strengthen cybersecurity policies to cover all aspects of digital life, including mobile device usage.