01 Oct Threat Hunting & AI In SOC | Ben McGavin, Justin Dolgos, Todd Willoughby (RSM) With Vladislav Babiuk
Posted at 11:14h
in Blogs
by Taylor Fox
Why you need to hear this episode of SOC Stars
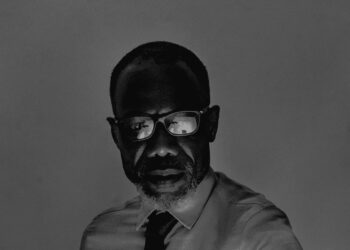
– Vladislav Babiuk, Director of Technical Product Marketing
San Jose, Calif. – Oct. 1, 2025

If you care about the future of cybersecurity, this episode of SOC Stars with RSM’s “Threat Hunting Dream Team” is a must-listen. In just 30 minutes, Vlad Babiuk of Stellar Cyber moderates a conversation that cuts through hype and gets real about how AI, automation, and human expertise are reshaping security operations centers (SOCs).
Why This Matters Right Now
The security landscape is shifting fast. NextGen SIEM, XDR, and AI-driven SOC tools are accelerating detection, yet cyber attackers keep evolving. The central question: where do human threat hunters fit in a world of autonomous SOCs?
This discussion answers that question head-on. You’ll learn why manual threat hunting isn’t obsolete—it’s more critical than ever—and how SOCs can combine AI scale with human judgment to stay ahead of adversaries.

ADVERTISEMENT
Key Takeaways You’ll Hear
- Human intuition vs. machine speed: Todd Wilby, Director at RSM, makes the case that AI is powerful, but only humans can interpret context, spot edge cases, and fine-tune detection rules.
- AI as a teammate, not a replacement: Ben, RSM’s threat hunting lead, explains why today’s AI tends to over-flag and under-contextualize. Without humans, SOCs risk drowning in false positives.
- The “haystack vs. the needle” problem: Justin describes how AI narrows the haystack of alerts, but only human oversight can determine malicious intent and business impact.
- Proactive defense in action: Learn how RSM blends Stellar Cyber’s automation with human hunting to move beyond reactive alerts—catching anomalies across login patterns, infrastructure traffic, and more.
- Agentic AI as a force multiplier: Concrete examples show how AI can act like a junior analyst, automatically pulling forensic data, building timelines, and enriching context—leaving humans to chase the deeper trails.
- Fighting burnout: SOC analysts face high turnover due to alert fatigue and repetitive tasks. AI reduces workload and highlights true anomalies, extending careers and improving morale.
- The future of threat hunters: Instead of being replaced, hunters will evolve into strategic investigators—leading hunts, modeling adversary intent, and steering AI systems toward what matters most.
Why Listen All the Way Through
This isn’t another abstract “AI in security” debate. The conversation is grounded in real frontline experience. Todd, Ben, and Justin share candid insights from operating SOCs that process hundreds of thousands of alerts each quarter. They explain exactly how automation is deployed, what works, and where human creativity remains irreplaceable.
By the end, you’ll understand:
- How to balance automation with human oversight.
- Why proactive hunting is the SOC differentiator of the future.
- How AI is changing analyst workflows—and making the job sustainable.
- What the role of the threat hunter will look like five years from now.
The Bottom Line
If you lead or work in a SOC—or simply want to understand where security operations are headed—this episode will sharpen your thinking. You’ll walk away with actionable insights on blending AI and human expertise, reducing alert fatigue, and building a SOC that’s not just reactive but resilient, proactive, and ready for tomorrow’s threats.
Invest 30 minutes. Gain a playbook for the next decade of cyber defense.
– Vladislav Babiuk, Director of Technical Product Marketing

 About Stellar Cyber
About Stellar Cyber
Stellar Cyber’s Open XDR Platform delivers comprehensive, unified security without complexity, empowering lean security teams of any skill level to secure their environments successfully. With Stellar Cyber, organizations reduce risk with early and precise identification and remediation of threats while slashing costs, retaining investments in existing tools, and improving analyst productivity, delivering an 8X improvement in MTTD and a 20X improvement in MTTR. The company is based in Silicon Valley. For more information, visit https://stellarcyber.ai.
Source link



 About Stellar Cyber
About Stellar Cyber