Endpoint Security
,
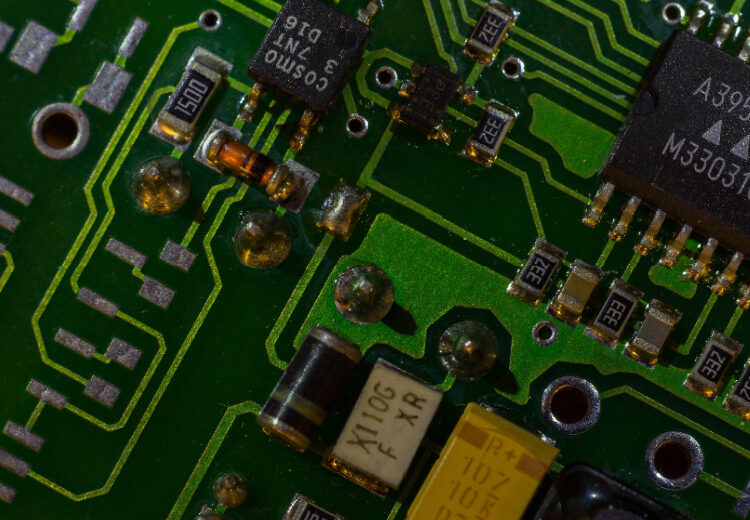
Hardware / Chip-level Security
Experts Detail Upsides of Bug Bounties and Getting Devices Into Researchers’ Hands
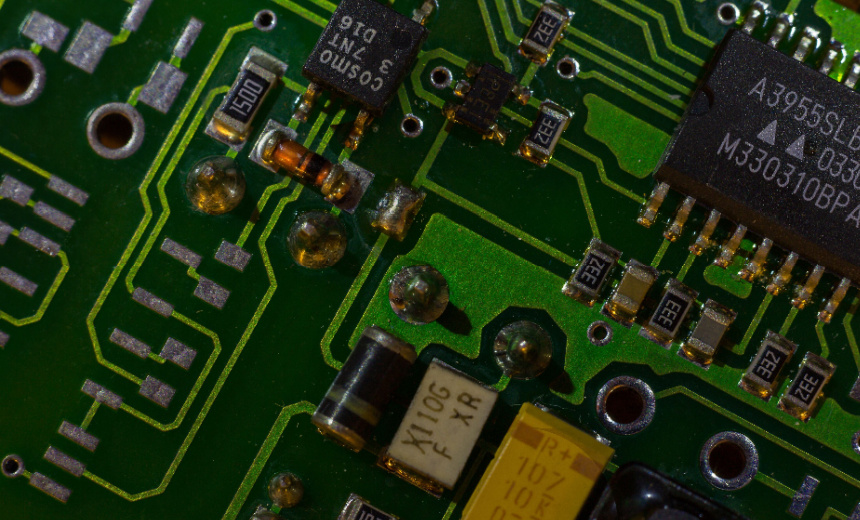
If hardware once had a reputation as an immutable root of trust, more than a decade of worries about compromised supply chains, side channel attacks and insecure enclaves have sanded that standing down to a stump.
See Also: Upgrade to a New AI Era at Work
Vulnerabilities are a fact of life – but how they end up in devices involves numerous factors. “I see hardware security vulnerabilities as a business problem with a business choice,” said Alex Guzman, CISO for Cisco Network Devices, speaking this week at the Hardware.io conference in Amsterdam. Information Security Media Group has invested in the conference.
“When you’re sourcing components and platforms that maybe are already out of date, or you choose a manufacturing model and you’re trying to go fast to market, you’re making decisions and trade-offs – fast to market or security, or not even considering security,” he warned the audience.
Security teams are and must continue to bridge that gap and “speak business language in terms of: Here’s the risk, and here’s why we need to solve it,” said Guzman, who also helps lead the OWASP Internet of Things Project, which aims to foster better understanding of IoT security issues and security decision-making.
How or if customers act on vulnerability patching and mitigation advice provided by vendors is another part of the equation.
“No one’s going to brush your teeth for you, right?” he said.
Veteran hardware hacker Adam Laurie, head of product security at electric-vehicle-charging firm Alpitronic, which manufactures electric vehicle chargers and sells them to charge point operators that badge the chargers with their name, regularly finds EV chargers exposed on the public internet. In many cases, his company will also have to remind the operators – as instructed when they first received the chargers – they need to change the initial password that shipped on the device.
It may seem Sisyphean to go through the same bad cybersecurity decisions year after year. Laurie gave a philosophical take, saying that lessons well-known in the security community require renewed emphasis anytime new technology arrives on the market. “I’ve been doing hardware or cybersecurity stuff for 30-odd years. I see the same lessons being learned over and over and over again. It’s an evolution.”
With so many new vulnerabilities in hardware, one question posed at the conference is whether vendors should be doing more.
Across multiple presentations at the event, many – although not all – speakers highlighted positive experiences with vendors. At least in some cases vendors were receptive to vulnerability reports and acted quickly to publish security alerts and firmware updates. Other manufacturers need additional prodding – as occurred when a well-known YouTube personality posted a widely watched video asking why a patch was so long in coming.
Some vendors put their money where their mouth is by pursuing bug bounty programs that they run or outsource to a third party to manage.
Some manufacturers sponsor hacking competitions, sometimes donating their own gear – for example, for Hardwear.io’s annual HardPwn challenge, which gives attendees the ability to hack well-known devices in return for prizes.
Featured devices this year included multiple offerings from Google, including the Pixel Phone 9a and also its TV Streamer, as well as Cisco’s MS130 and MS150 switches, plus numerous access points, as well as devices from at least vendor that asked to not be publicly named.
The competition revealed new vulnerabilities in some devices already reported to the relevant manufacturers. More flaws could come to light in the coming weeks since participants were able to take some devices away with them for further testing.
Vendors said hands-on pen testing needn’t be a one-time experience. Cisco told attendees that if there’s enterprise or industrial internet-of-things gear they want to get their hands on, and they have the hardware hacking bona fides, they’ll do everything they can to make that happen.
Justin Searle, director of ICS security at InGuardians and a long-time industrial control system and operational technology security trainer, said a recommendation he often gives to makers of big critical infrastructure products is to operate an invite-only bug bounty program for vetted members of the community. Whatever type of bug bounty program being run, it doesn’t necessarily need to feature cash rewards, but can instead offer useful equipment – soldering machine stations, for example – or fun swag.