A hidden danger has been lurking in the Go programming ecosystem for over four years.
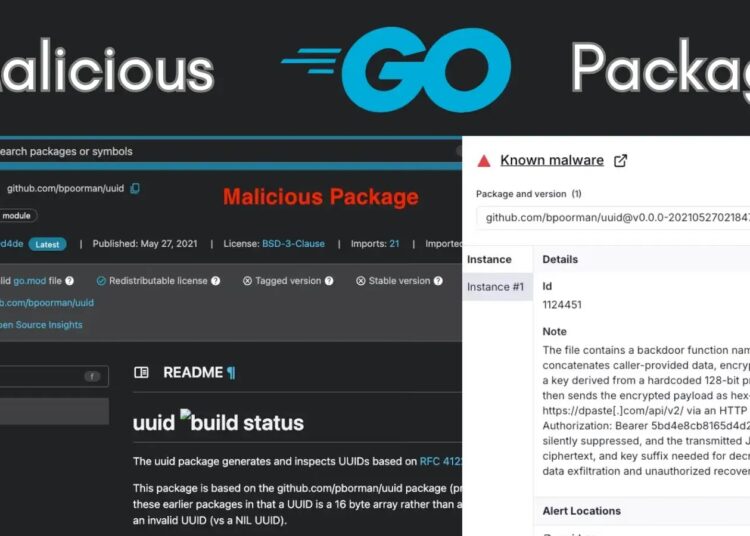
Security researchers from the Socket Threat Research Team have discovered two malicious software packages that impersonate popular Google tools.
These fake packages, designed to trick busy developers, have been quietly stealing data since May 2021.
![Socket AI Scanner’s analysis of the malicious github[.]com/bpoorman/uuid package](https://gbhackers.com/wp-content/uploads/2025/12/image-26.png)
The malicious packages are identified as github.com/bpoorman/uuid and github.com/bpoorman/uid.
They are designed to look almost identical to the legitimate and widely used pborman and Google UUID libraries.
These real libraries are the industry standard for generating unique identifiers for database rows, user sessions, and job tracking.
The “Typosquatting” Trap
The attacker, using the username “bpoorman,” used a technique called “typosquatting.”
By choosing a name visually similar to “pborman” (a legitimate maintainer), the attacker hoped developers would mistype the name or fail to notice the difference in a long list of dependencies.
![page for the malicious github[.]com/bpoorman/uuid Go package](https://gbhackers.com/wp-content/uploads/2025/12/image-27-1024x458.png)
github[.]com/bpoorman/uuid Go packageCrucially, the fake software actually works. It generates unique IDs just like the real version. This allows it to stay hidden, as the application does not crash or show obvious errors. However, the fake code contains a secret backdoor.
The malicious code includes a helper function named Valid. In the legitimate software, developers might expect a function with this name to check if an ID is formatted correctly. In the fake version, it does something much more dangerous.
When a developer passes data into this Valid function such as user IDs, email addresses, or even session tokens the code secretly encrypts that information.
It then sends the stolen data to dpaste.com, a public text-sharing website, using a hardcoded API token. The attacker can then retrieve this data anonymously.
Because the data is encrypted before it leaves the victim’s computer, standard security tools might not notice that sensitive secrets are being stolen.
Despite being published years ago, these packages have remained available on the Go package discovery site and public mirrors.
![Excerpt from the threat actor’s github[.]com/bpoorman/uid repository showing the uid.go exfiltration code](https://gbhackers.com/wp-content/uploads/2025/12/image-28-1024x580.png)
github[.]com/bpoorman/uid repository showing the uid.go exfiltration code While the public index shows “0 imports,” researchers warn that this is misleading.
The index does not count downloads from private corporate repositories or internal tools, meaning the actual number of affected systems is unknown.
Socket has reported both packages to the Go security team and requested that the author’s account be suspended.
Developers are strongly advised to audit their projects and ensure they are using github.com/google/uuid or github.com/pborman/uuid, and not the malicious “bpoorman” imposter.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.