Mobile apps often surface security risks earlier than other enterprise systems. Because mobile app code ships publicly through app stores, attackers can download, reverse engineer and analyze it, gaining a head start in finding data leaks and security vulnerabilities. For mobile AppSec and DevSecOps leaders, this reality makes mobile app security a critical focus for 2026.
Here are the top five mobile app security threats shaping 2026.
1. AI Discovery Through SDKs & Third Parties
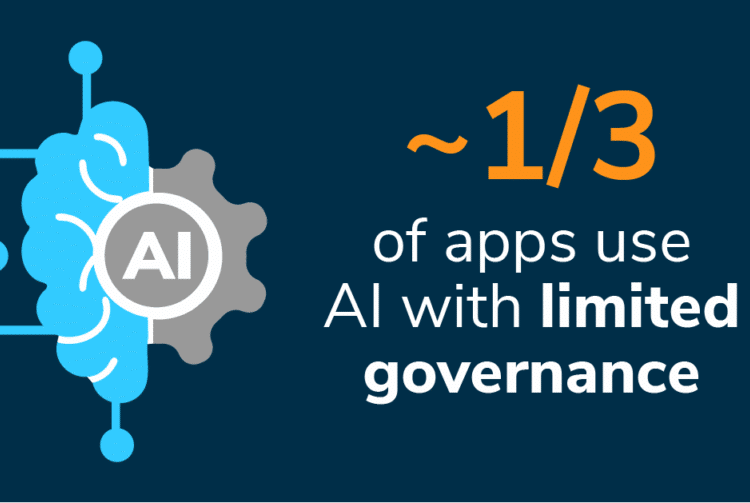
AI increasingly enters mobile apps through third-party SDKs and updates, not just through code developers intentionally write. It often comes packaged inside analytics libraries and third-party services teams already trust.
“What happens when the tens, hundreds or thousands of apps you’ve vetted suddenly incorporate AI through third-party SDKs? Overnight, your AI governance falls apart.”
— NowSecure Co-Founder Andrew Hoog
Mobile teams struggle to answer a simple question: Which apps actually use AI, and how?
Why this accelerates in 2026:
- Third-party SDKs quietly embed AI features
- SaaS-based AI processing hides behind backend services
- Enterprise AI governance rarely includes mobile dependency analysis
What mobile security teams should do now:
- Inventory AI usage across mobile apps
- Differentiate on-device AI from SaaS-based AI
- Validate findings with evidence suitable for audits and governance reviews.
NowSecure data shows that roughly one-third of assessed mobile apps already contain AI components, and that number keeps climbing.

2. Post-Quantum Cryptography (PQC) Gaps
Quantum computing may not dominate production systems yet, but adversaries already plan ahead.
“With how cheap storage has become, it’s effectively assumed that large governments scoop up encrypted data to harvest now and decrypt later.”
— Andrew Hoog
Attackers can collect encrypted mobile data now, store it cheaply and decrypt it later when quantum capabilities mature.
Why mobile matters:
- Mobile apps handle long-lived, high-value data:
- financial records
- healthcare information
- identity and authentication material
- Legacy cryptography still appears widely in production apps
What mobile security teams should do now:
- Inventory cryptographic methods inside mobile apps.
- Identify legacy algorithms that won’t survive PQC transitions.
- Plan for multi-release updates, not one-time crypto swaps.
Banks and public-sector organizations already ask these questions. Preparing early helps mobile teams reduce future rework.
3. Mobile Supply-Chain Attacks
Supply-chain attacks continue to dominate breach headlines because they scale effortlessly across apps.
Two patterns keep repeating:
- You rely on vendor X → vendor X gets compromised
- You rely on open source → a dependency turns hostile (NPM, downstream dependencies, shared frameworks)
Why mobile amplifies impact:
- SDK reuse spreads risk across dozens or hundreds of apps.
- Mobile updates distribute malicious code at scale.
- Detection often trails exploitation.
What mobile security teams should do now:
- Track mobile dependencies continuously, including SDKs and open-source libraries.
- Monitor supply-chain vulnerabilities that impact mobile apps and the APIs they rely on.
- Verify exposure and respond quickly as new mobile supply chain incidents emerge.
In 2026, mobile supply-chain risk won’t hinge on whether an app gets compromised, but on how quickly teams detect exposure and respond. Treating dependency tracking as a continuous discipline rather than a one-time review limits the blast radius when the next incident hits.
Everything you put into your mobile app becomes public. Expect attackers to examine it.
4. Privacy Risk: Third-Party Data Flow, App Store Delays, Regulation
Privacy failures increasingly block releases, trigger audits and invite enforcement.
Why pressure increases in 2026:
Mobile apps frequently expose privacy risk before legal or compliance teams see it.
What mobile security teams should do now:
- Map actual data flows in mobile apps, not just documented disclosures.
- Identify third-party data sharing that creates approval, compliance or regulatory risk.
- Fix privacy issues before release to avoid app store delays and enforcement action.
Mobile app privacy testing helps organizations surface privacy risk early and avoid costly release delays or enforcement.
5. Reconnaissance and Automated Attacks
Mobile apps publish their code publicly, giving attackers the same visibility as defenders while automation adds to their advantage.
“Everything you put into your mobile app becomes public. Expect attackers to examine it just as we do when we adopt offensive methodology to perform pen testing.”
— Andrew Hoog
Open-source tools such as Frida and Radare, along with powerful automated analysis tools such as NowSecure Workstation, aid reverse engineering, allowing attackers (and defenders) to quickly identify weaknesses and chain exploits together. This process routinely exposes hardcoded cryptography, URLs and secrets, reveals forgotten and undocumented endpoints and surfaces debugging symbols developers never intended to share publicly.
These flaws are not theoretical. They directly enable automated phishing campaigns, credential harvesting, account takeover and lateral movement inside enterprise systems — patterns repeatedly observed across real-world breaches and highlighted in the NowSecure research “525,600 Assessments Later — Top Mobile App Risks Since 2022.”
What mobile security teams should do now:
- Assume attackers already understand your app.
- Remove reconnaissance enablers, including:
- hardcoded values
- exposed internal APIs
- weak authentication flows
- Reduce attacker time-to-exploit, not just vulnerability counts.
This year, reconnaissance will continue to fuel mobile attacks. Teams that limit what attackers can learn from mobile apps can break attack chains early before exploitation escalates.
Why Mobile Security Leads in 2026
Across AI, cryptography, supply chains, privacy and reconnaissance, one reality keeps showing up: Mobile apps surface risk earlier than any other part of the enterprise. Teams that treat mobile AppSec as a source of real-world signal — not just another testing checkbox — gain visibility others don’t.
In 2026, the advantage won’t come from guessing where risk lives; it will come from recognizing it first and acting on it.