21 Nov AI-Powered Cyberattacks & Social Engineering. How to Detect and Defend Against Them.
in Blogs
This week in cybersecurity from the editors at Cybercrime Magazine
![]() Sausalito, Calif. – Nov. 21, 2025
Sausalito, Calif. – Nov. 21, 2025
– Watch the YouTube video
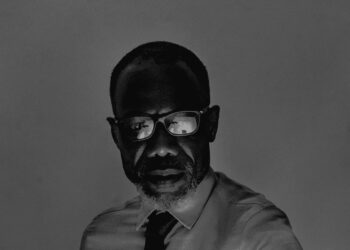
Fortune 500 chief information security officer Adam Keown says that “when it comes to artificial intelligence, we have to quit thinking of deepfakes or voice AI as a Hollywood special effect, and that we’re one step away from a help desk ticket waiting to happen now.”
Keown, CISO at Kingsport, Tenn.-based Eastman, a global specialty materials company with around 14,000 employees, adds, “Unfortunately, these AI capabilities are creating a low barrier of entry. It’s really democratized sophisticated attack capabilities so that the script kiddies can use them and not only harm enterprises but also harm people in their personal lives.”
In the war against cybercrime, Doppel is arming organizations with the knowledge and a platform to defend and protect brands and their people from AI-powered cyberattacks and social engineering. Their CEO, Kevin Tian, explains how in a recently released video on the award-winning Cybercrime Magazine YouTube channel.
“We’re giving you the tools that the bad guys have to test your organization,” says Tian. Apparently, his message is resonating with its target audience. Doppel protects dozens of the Fortune 500, notable brands including Coinbase, Ramp, Commerce, and Orrick, and over 200 total customers in industries such as financial services, energy and utilities, technology and software, industrial and manufacturing, healthcare and life sciences, and media.
Watch the Video
Cybercrime Magazine is Page ONE for Cybersecurity. Go to any of our sections to read the latest:
- SCAM. The latest schemes, frauds, and social engineering attacks being launched on consumers globally.
- NEWS. Breaking coverage on cyberattacks and data breaches, and the most recent privacy and security stories.
- HACK. Another organization gets hacked every day. We tell you who, what, where, when, and why.
- VC. Cybersecurity venture capital deal flow with the latest investment activity from various sources around the world.
- M&A. Cybersecurity mergers and acquisitions including big tech, pure cyber, product vendors and professional services.
- BLOG. What’s happening at Cybercrime Magazine. Plus the stories that don’t make headlines (but maybe they should).
- PRESS. Cybersecurity industry news and press releases in real time from the editors at Business Wire.
- PODCAST. New episodes daily on the Cybercrime Magazine Podcast feature victims, law enforcement, vendors, and cybersecurity experts.
- RADIO. Tune into WCYB Digital Radio at Cybercrime.Radio, the first and only round-the-clock internet radio station devoted to cybersecurity.
Contact us to send story tips, feedback and suggestions, and for sponsorship opportunities and custom media productions.