Cybersecurity researchers are calling attention to a new campaign that delivers the Astaroth banking trojan that employs GitHub as a backbone for its operations to stay resilient in the face of infrastructure takedowns.
“Instead of relying solely on traditional command-and-control (C2) servers that can be taken down, these attackers are leveraging GitHub repositories to host malware configurations,” McAfee Labs researchers Harshil Patel and Prabudh Chakravorty said in a report.
“When law enforcement or security researchers shut down their C2 infrastructure, Astaroth simply pulls fresh configurations from GitHub and keeps running.”
The activity, per the cybersecurity company, is primarily focused on Brazil, although the banking malware is known to target various countries in Latin America, including Mexico, Uruguay, Argentina, Paraguay, Chile, Bolivia, Peru, Ecuador, Colombia, Venezuela, and Panama.

This is not the first time Astaroth campaigns have trained their sights on Brazil. In July and October 2024, both Google and Trend Micro warned of threat clusters dubbed PINEAPPLE and Water Makara that used phishing emails to distribute the malware.
The latest attack chain is no different in that it also begins with a DocuSign-themed phishing email containing a link that downloads a zipped Windows shortcut (.lnk) file, which, when opened, installs Astaroth on the compromised host.
The LNK file incorporates obfuscated JavaScript that’s responsible for fetching additional JavaScript from an external server. The newly fetched JavaScript code, for its part, downloads a number of files from one of the randomly selected hard-coded servers.
This includes an AutoIt script that’s executed by the JavaScript payload, following which it loads and runs shellcode, which, in turn, loads a Delphi-based DLL to decrypt and inject the Astaroth malware into a newly created RegSvc.exe process.
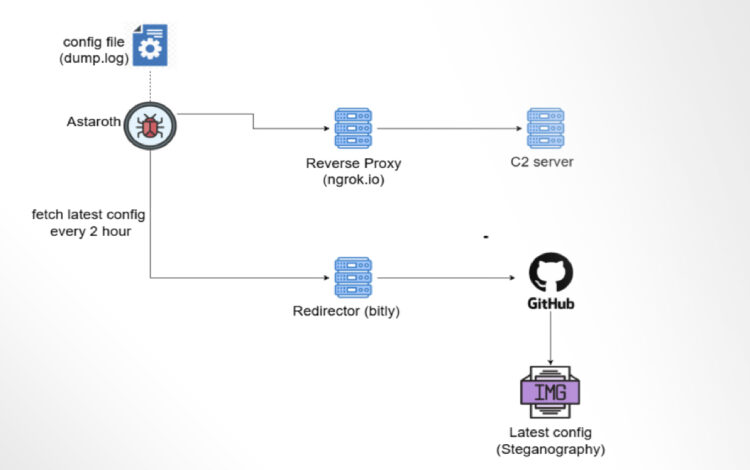
Astaroth is a Delphi malware designed to monitor victims’ visits to banking or cryptocurrency websites and steal their credentials using keylogging. The captured information is transmitted to the attackers using the Ngrok reverse proxy.

It accomplishes this by checking the active browser program window every second and whether it has a banking-related site opened. If these conditions are met, the malware hooks keyboard events to record keystrokes. Some of the targeted websites are listed below –
- caixa.gov[.]br
- safra.com[.]br
- itau.com[.]br
- bancooriginal.com[.]br
- santandernet.com[.]br
- btgpactual[.]com
- etherscan[.]io
- binance[.]com
- bitcointrade.com[.]br
- metamask[.]io
- foxbit.com[.]br
- localbitcoins[.]com

Astaroth also comes fitted with capabilities to resist analysis and shuts down automatically if it detects emulator, debugger, and analysis tools like QEMU Guest Agent, HookExplorer, IDA Pro, ImmunityDebugger, PE Tools, WinDbg, and Wireshark, among others.
Persistence on the host is set up by dropping an LNK file in the Windows Startup folder that runs the AutoIT script to launch the malware automatically upon a system reboot. What’s more, not only is the initial URL accessed by the JavaScript within the LNK file geofenced, the malware also makes sure that the machine’s system locale is not set to English or the U.S.
“Astaroth uses GitHub to update its configuration when the C2 servers become inaccessible, by hosting images on GitHub, which uses steganography to hide this information in plain sight,” McAfee said.
In doing so, the malware leverages a legitimate platform to host configuration files and turn it into a resilient backup infrastructure when primary C2 servers become inaccessible. The company noted that it worked with the Microsoft-owned subsidiary to remove the GitHub repositories, temporarily neutralizing the operations.