A vulnerability has been found in the very popular, free file-compressing tool 7-Zip. The flaw, tracked as CVE-2025-11001, has a public exploit, leading to a high-risk warning from the UK’s NHS England Digital.
While the NHS confirmed active exploitation has not been observed in the wild, the public PoC means the risk of future attacks is extremely high. The vulnerability was discovered by Ryota Shiga of GMO Flatt Security Inc., with help from their AI tool AppSec Auditor Takumi.
What’s the Problem?
The issue is related to how older 7-Zip versions handle symbolic links inside ZIP files (a symbolic link is a shortcut to another file or folder). As explained by Trend Micro’s Zero Day Initiative (ZDI), which first revealed the vulnerability last month, it is a Directory Traversal RCE flaw.
This means, a specially made ZIP file can trick the program into traversing (moving) to unauthorised system directories during extraction, allowing an attacker to run unwanted programs or “execute arbitrary code.” The issue has a CVSS risk score of 7.0 (High), and exploiting it requires user interaction (the target must open the malicious ZIP file).
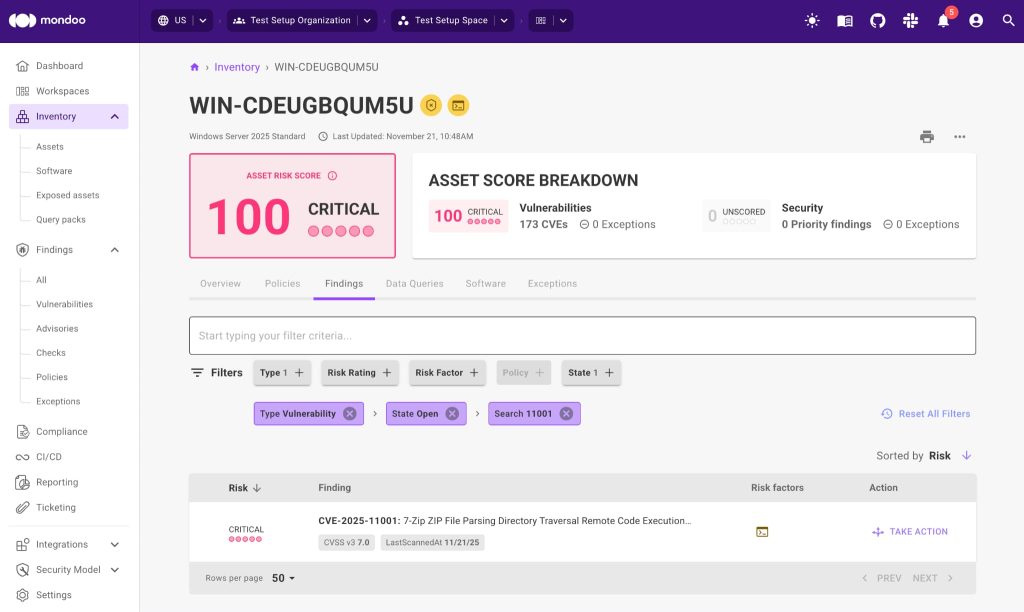
According to a blog post from vulnerability detection platform Mondoo, this flaw is particularly dangerous for three reasons. First, the extraction of a malicious ZIP can allow an attacker to run code using a high-level account, such as a service account or privileged user, possibly leading to a full system takeover. Second, it is relatively easy to exploit (only requiring a user to open the archive), and third, 7-Zip’s widespread use provides a vast attack surface of unpatched systems.
Microsoft Flags Activity Linked to CVE 2025 11001
The danger level increased dramatically when security researcher Dominik (known online as pacbypass) publicly shared a working proof-of-concept (PoC) exploit. This ready-to-use code provides cybercriminals with an easy blueprint for attacks, likely speeding up the spread of attacks. This flaw affects only Windows systems and is most critical when files are extracted under highly privileged accounts, which can lead to a full system takeover.
Microsoft has tracked malicious activity linked to this vulnerability under the label Exploit:Python/CVE 2025 11001.SA!MTB, a detection name rather than a family title, yet it still shows active use of the public code in malware campaigns.
How to Stay Safe
The issue was fixed with version 25.00 in July 2025. However, as Dominik Richter, CPO and Co-founder of Mondoo, told Hackread.com, the software lacks an internal update mechanism; therefore, updates must be performed manually by the user or managed through enterprise tools, scripts, or deployment systems like Microsoft Intune.
This lack of automated patching “means that it’s highly likely that many systems are still running the older version that is vulnerable to this CVE,” Richter noted.
To update manually, users must find all 7-Zip installations older than version 25.00 on Windows machines and promptly install the current version, 25.01. Or, download the latest version from 7-Zip’s official download page.















