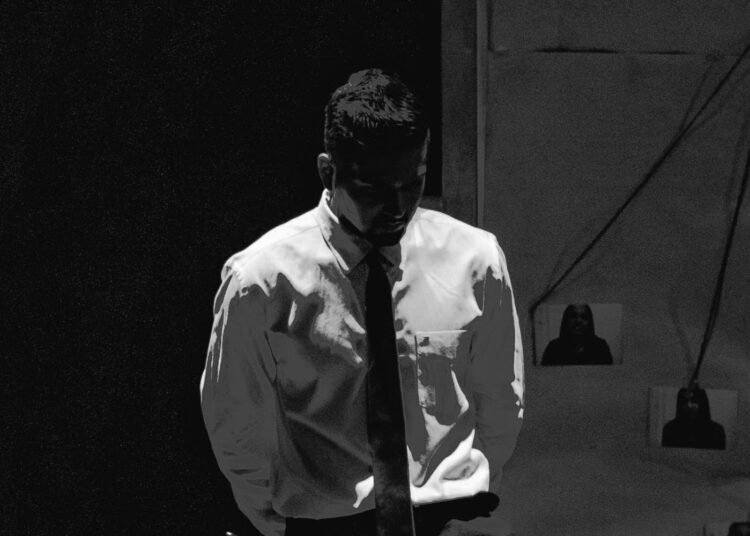
“As an AI entrepreneur and cybersecurity leader, I’ve watched compliance frameworks struggle to keep pace with modern threats,” writes Nishant Sonkar, Global Cloud Compliance Lead at Cisco, in a Forbes article.
Recent research shows that:
Ninety-eight percent of organizations have at least one third‑party vendor that has suffered a data breach. Attackers often compromise suppliers first and move laterally into larger enterprises.
At least 35.5 percent of data breaches in 2024 originated from third‑party compromises, up 6.5 percentage points from 2023.
Seventy-two percent of data breaches involve data stored in the cloud, and 30 percent span multiple environments.
According to IBM, the average cost of a breach reached $4.88 million in 2024.
According to Cybersecurity Ventures (via Cybercrime Magazine), by 2025, the global cost of cybercrime is projected to hit $10.5 trillion.
These numbers illustrate why passing an audit isn’t enough. In a cloud‑first, vendor‑heavy world, governance must be embedded into architecture, automation and accountability. Checklists alone cannot prevent breaches in a live environment.
For Sonkar, his own Common Control Framework (CCF) overhaul at Cisco was about designing resilience at scale. He believes that leaders who view governance as a dynamic capability will not only pass audits but also prevent crises before they occur.
Read the Full Story