A Dutch TV and radio broadcaster has found itself at the mercy of cybercriminals after suffering a cyber attack, and leaving it scrambling to find ways to play music to its listeners.
RTV Noord, which provides TV and radio programming in the northern province of Groningen in the Netherlands, discovered it had been hacked on November 6, 2025.
On Thursday morning, staff on the “De Ochtendploeg” breakfast show discovered their access to computer systems was blocked, forcing them to resort to manually playing CDs, and even putting LP vinyl records on a turntable to keep listeners entertained.
By the following morning, the broadcaster had begun publishing updates on its news website and app again – for “extremely major news” at least.
Although the precise nature of the hack against RTV Noord has not been disclosed, it would be a brave person who bet against it being a ransomware attack.
RTV Noord confirmed that the attackers left a message on its network, though it has not been made public.
Given the disruption and the trend in similar incidents, the obvious suspicion is that this was a ransom note demanding payment for decryption or to prevent stolen data being leaked.
That being said, it’s always possible that whoever has compromised the broadcaster has not done so with a financial motivation. In the past, for instance, there have been TV and radio stations that have found themselves hacked for political reasons.
Regardless of motive, hacking a broadcaster can have serious repercussions which go beyond the financial. RTV Noord is not just providing television and radio services to the local population – it also acts as an official emergency broadcaster that provides information to citizens in the event of a disaster or crisis.
In a brief statement, RTV Noord said that its newsroom could only be “reached via WhatsApp” — a clear indication that internal communications systems were either inaccessible or untrustworthy during the incident.
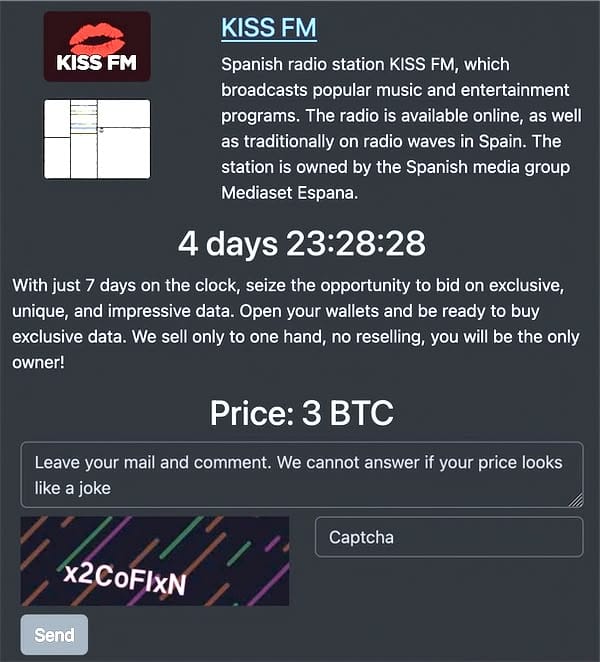
Coincidentally – or perhaps not – the attack on RTV Noord became public on the same day that the Rhysida ransomware gang claimed responsibility for an attack on Spanish radio station KISS-FM, offering its stolen data for approximately US $300,000 worth of Bitcoin.
Broadcasters like RTV Noord have increasingly become targeted by cybercriminals hoping to amplify their notoriety. In past years similar attacks have managed to impact many other stations, sometimes even knocking programmes off the airwaves, or broadcasting bogus warnings about missile strikes.
Broadcast infrastructure is both public-facing and time-critical. Even short-term disruption is reputationally damaging and can cascade into real-world harm, especially when broadcasters have emergency notification responsibilities. And that’s exactly the kind of leverage that a ransomware group loves to have at its disposal.















