Cybersecurity researchers have discovered vulnerable code in legacy Python packages that could potentially pave the way for a supply chain compromise on the Python Package Index (PyPI) via a domain takeover attack.
Software supply chain security company ReversingLabs said it found the “vulnerability” in bootstrap files provided by a build and deployment automation tool named “zc.buildout.”
“The scripts automate the process of downloading, building, and installing the required libraries and tools,” security researcher Vladimir Pezo said. “Specifically, when the bootstrap script is executed, it fetches and executes an installation script for the package Distribute from python-distribute[.]org – a legacy domain that is now available for sale in the premium price range while being managed to drive ad revenue.”
The PyPI packages that include a bootstrap script that accesses the domain in question include tornado, pypiserver, slapos.core, roman, xlutils, and testfixtures.

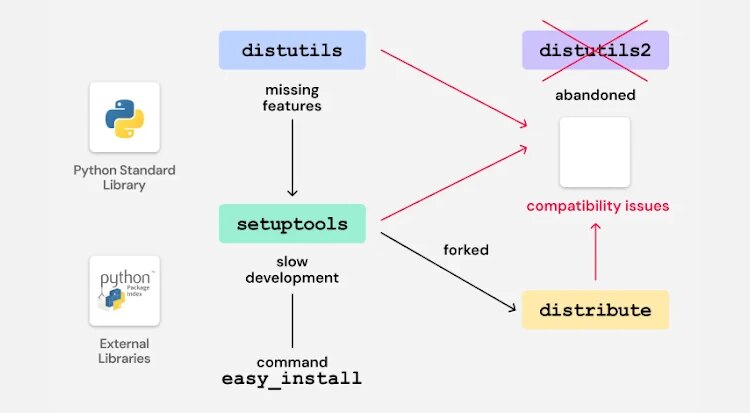
The crux of the problem concerns an old bootstrap script (“bootstrap.py”) that was used along with the zc.buildout tool to initialize the Buildout environment. The Python script also supported the ability to install a packaging utility called “Distribute,” a short-lived fork of the Setuptools project, into the local environment.
To achieve this, the Distribute installation script (“distribute_setup.py”) is fetched from the python-distribute[.]org, a domain that has been up for sale since 2014. In adding the option, the idea was to instruct the bootstrap script to download and install the Distribute package instead of the older Setuptools package to manage eggs and dependencies for the buildout.
It’s important to note that the Distribute fork came into being due to the lack of active development of Setuptools, the main package management tool used at that time. However, the features from Distribute were integrated back into Setuptools in 2013, rendering Distribute obsolete.
The issue identified by ReversingLabs concerns the fact that many packages have continued to ship the bootstrap script that either attempts to install Distribute by default or when the command-line option (“-d” or “–distribute”) is specified. This, coupled with the fact that the domain in question is up for grabs, puts users at latent risk as an attacker could weaponize this setup to serve malicious code when the bootstrap script is inadvertently run and potentially steal sensitive data.
While some of the affected packages have taken steps to remove the bootstrap script, the slapos.core package still continues to ship the vulnerable code. It’s also included in the development and maintenance version of Tornado.
Another important aspect to consider here is that the bootstrap script is not executed automatically during the package installation and is written in Python 2. This means the script cannot be executed with Python 3 without modifications. But the mere presence of the file leaves an “unnecessary attack surface” that attackers can exploit if developers are tricked into running code that triggers the execution of the bootstrap script.
The threat of a domain takeover is not theoretical. In 2023, it came to light that the npm package fsevents was compromised by a bad actor who seized control of an unclaimed cloud resource hosted at fsevents-binaries.s3-us-west-2.amazonaws[.]com to push malicious executables to users installing certain versions of the package (CVE-2023-45311, CVSS score: 9.8).

“The issue lies in the programming pattern that includes fetching and executing a payload from a hard-coded domain, which is a pattern commonly observed in malware exhibiting downloader behavior,” Pezo said. “The failure to formally decommission the Distribute module allowed vulnerable bootstrap scripts to linger and left unknown numbers of projects exposed to a potential attack.”
The disclosure comes as HelixGuard discovered a malicious package in PyPI named “spellcheckers” that claims to be a tool for checking spelling errors using OpenAI Vision, but contains malicious code that’s designed to connect to an external server and download a next-stage payload, which then executes a remote access trojan (RAT).
The package, first uploaded to PyPI on November 15, 2025, by a user named leo636722, has been downloaded 955 times. It’s no longer available for download.
“This RAT can receive remote commands and execute attacker-controlled Python code via exec(), enabling full remote control over the victim’s host,” HelixGuard said. “When the user installs and runs the malicious package, the backdoor becomes active, allowing the attacker to remotely control the user’s computer.”