 It seems like only yesterday that LockBit 5.0 announced, with its usual hubris, a “new secure blog domain, with a multi-layered protection system against all-powerful FBI agents.”
It seems like only yesterday that LockBit 5.0 announced, with its usual hubris, a “new secure blog domain, with a multi-layered protection system against all-powerful FBI agents.”
And it seems like only yesterday that Rakesh Krishnan revealed LockBit 5’s IP address and domain.
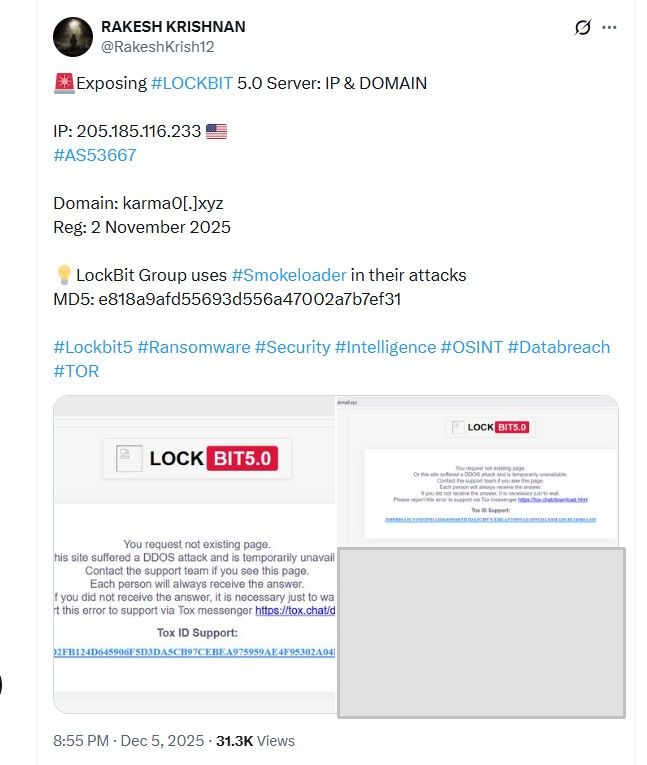
In a post on X.com on December 5, @RakeshKrish12 wrote:
Exposing #LOCKBIT 5.0 Server: IP & DOMAIN
IP: 205.185.116.233
#AS53667Domain: karma0[.]xyz
Reg: 2 November 2025LockBit Group uses #Smokeloader in their attacks
And as DataBreaches had also spotted and noted on LinkedIn, LockBit 5.0 was re-posting old data. Krishnan also tweeted:
- On 4th December 2025; the group had announced 23 new victims on their DLS, by scrapping old Data leaks [sic]
- Upon analyzing, it is found that 11 victims are recycled from April 2025 LockBit Leaks
- 2 Victims are from #Weyhro and #RansomHouse Group
This has not been an exactly impressive update for LockBit 5.
Cyber Security News provides additional details on the domain registration and the site’s security, including:
Scans reveal multiple open ports on 205.185.116.233, including vulnerable remote access, exposing the server to potential disruption.
…. This exposure highlights ongoing opsec failures for the group, disrupted multiple times, yet persistent. Defenders should block the IP and domain immediately; researchers can monitor for further leaks.















