Earlier in 2025, I was pleased to be at Bletchley Park with my colleagues who had been working on the TAIBOM project for my company. As part of this work, we had to choose two AI models to develop that would be used for testing of the various different features for the security of future AI. More on this can be found on the TAIBOM site, but this is not really the purpose of this blog.
The talk was really the follow-on from this blog I wrote at the end of 2023 on my research into a mysterious document. Eventually that led to the work I’m doing now – a lot in my spare time, but we’ve also been able to combine it with our day-to-day security work for the TAIBOM project which has been great.
The talk I gave touches on some of the many side-quests that I’ve found along the way – either through documents I’ve discovered or have been sent, or to the many famous historical figures who used shorthand from the 17th century (even up to today!). There were also a multitude of shorthands from different authors that looked very similar, so this has been a big challenge – and continues to be for all students of this subject. I am trying to keep track of what I find and I hope to begin steadily posting some of these interesting subjects which range from the Quakers through to the subject of alchemy!
We’ve been creating various datasets to support the model that we’ve developed in a very structured way (we have invented our own digital standard for this) – indeed, there will be multiple models for different shorthand dictionaries and some other logographic datasets.
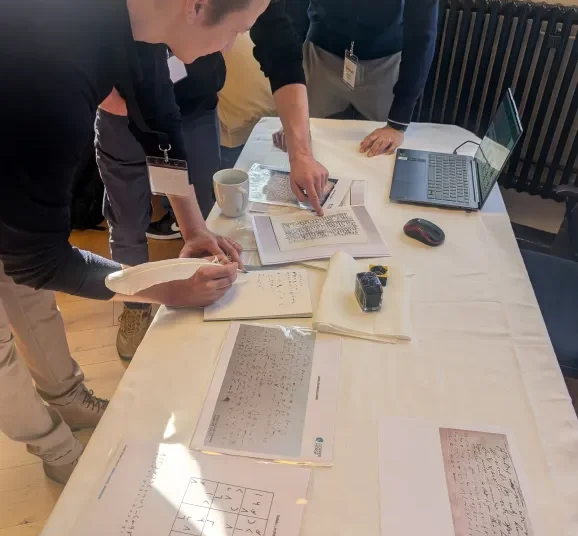
The picture shows some of my team demonstrating to people at Bletchley Park the Thomas Shelton model, so they people can try writing symbols of words and see if our model can recognise it. Thomas Shelton’s shorthand was used by Samuel Pepys for his diary (and his day-to-day business).

So watch this space – I’ll probably put up a separate area of the site to cover this subject.