Today marks the launch of the Code of Practice for Consumer IoT Security following a period of public consultation. You can find out more on the Department for Digital, Culture, Media & Sport’s (DCMS) website. The publication also means that the UK is now way ahead of the rest of the world in terms of leadership on improving IoT security and privacy.
As the original and lead author of the Code of Practice, I was really pleased to read the feedback and see that many other people feel the same way about improving the situation globally. I was able to discuss the feedback at length with colleagues from DCMS, the National Cyber Security Centre (NCSC) and other departments to ensure that we were creating a sensible measured set of guidance that took into account the needs and concerns of all stakeholders.
For further details on what the Code of Practice contains and why it exists, have a look at some of my previous blogs on this topic:
A number of other documents are being released today, all of which are well worth a read if you’re interested in this space.
Mapping Recommendations and Standards in the IoT security and privacy space
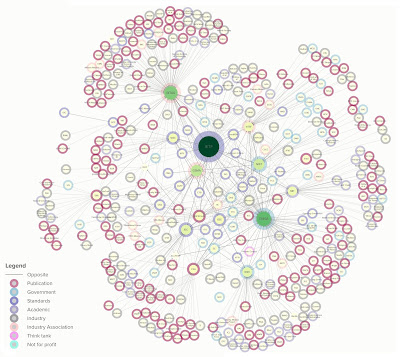
The thing that my team and I spent the most effort on over the summer period was mapping existing recommendations on IoT security and privacy from around the world against the Code of Practice. This was no mean feat and meant going through thousands of pages of pretty dry text. If you talk to anyone in the industry space, it is a job that everyone knew needed doing but nobody wanted to do it. Well I can say it is done now (thank you Ryan and Mark particularly!), but things like this are the never ending task. While we were working on it, new recommendations were being released and inevitably, just after we’d completed our work others were published. Equally, we ran the risk of mapping the entirety of the technical standards space. For now at least, we’ve stopped short of that and I think we’ve given implementers enough information such that they’ll be able to understand what commonalities there are across different bodies and where to look. I still am sufficiently sane to state that I’ll commit to keeping this updated, but we’ll let the initial dataset be used by companies first. Ultimately I’m hoping this is the tool that will aid defragmentation in the IoT security standards space and again I’ll continue to support this effort.
I’m really pleased that the government agreed with the suggestion that we should make the mappings available as open data. We’ve also created visual mappings just to make things a little more readable. All of this is hosted at https://iotsecuritymapping.uk which is now live.
 |
| Mapping recommendations to the UK’s Code of Practice for Consumer IoT Security |
Talking about the Code of Practice
I also continued to spend time discussing what we were doing with various security researchers and presented at both B-SidesLV in Las Vegas and at 44con in London. I also spoke to a number of different industry groups to explain what we were doing and what is happening next.
 |
| Most IoT products v Skilled hackers |
I often used this picture, partly because it is of my cat Pumpkin, partly because it illustrates the reality of most companies that are looking to digitise their products. Their new shiny connected products are on the left protected by not a lot, whilst the skilled attackers sit ready to pounce. The mobile industry has been in a cat and mouse game (stay with me here) with hackers and crackers for around 20 years now. Broadly speaking, the mobile device is a hard target and there are some great engineers working in product security across the mobile industry. Take then the washing machine industry, just as an example. What experience does a company that produces washing machines have in device and internet security? Very little is the answer. Startups are encouraged to ship unfinished products and there is a continued prevailing attitude that companies can get away with doing and spending very little on security. It is no surprise that these products are easily broken and cause consumers significant security and privacy harm, further degrading consumer trust overall in connected products.
No more. Change is here.